Cloud Architecture Planning
When it comes to planning your cloud architecture and cloud security architecture, it's all about how the components of the cloud work together to provide you with a tailored and highly secure cloud solution. Whether it's virtual machines, container infrastructures, or migrating on-premise infrastructures to the cloud, we have accompanied hundreds of IT teams in building their cloud environments and know what matters in cloud architecture planning.
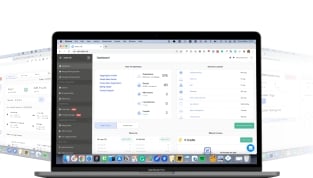
How Xelon Cloud Architecture Planning for your business works with Xelon
Assessing your needs
As a first step of your cloud migration, our team of experienced Cloud Architects works closely with you to determine the most suitable type of cloud for your company. Together, we define which data and systems are to be integrated into the chosen private, public, or hybrid cloud solution
Defining the Cloud Security Architecture
After the needs analysis, we will design a tailor-made Cyber Security Strategy for your cloud solution, i.e. Cloud Security Architecture. With the appropriate security measures in place, you can rest assured that your system will be safeguarded against any potential hacker attacks.
Migrating into the Cloud
In many cases, the biggest challenge when it comes to cloud migrations is transferring data from the existing IT environment to the cloud. That's where our team of experienced Cloud Architects comes in. We are here to support you in seamlessly mapping your IT environments into Public, Private or Hybrid Clouds.
Monitoring
Following the migration to the cloud our team of expert Cloud Architects is monitoring your cloud environment continuously. With their expertise, we can guarantee that the migration and integration of your data and systems into the cloud were executed flawlessly.
Why Cloud-native Architectures are becoming more important
"Cloud-native architectures are currently one of the most important cloud trends. These architectures are specifically designed for the cloud. IT operations teams appreciate the scalability, flexibility, and cost-effectiveness of cloud-native architectures. The IT environment has become a crucial factor in workplace design, aiding IT companies in attracting and retaining ICT professionals. With a cloud-native architecture, your IT talents can fully maximize their potential.
Ivan Fischer
Head of Sales, Xelon AG
Our customers
/Blue_Light/ASE_235x103_blue_light.png?width=235&height=103&name=ASE_235x103_blue_light.png)
/Blue_Light/EFK_235x103_blue_light.png?width=235&height=103&name=EFK_235x103_blue_light.png)
/Blue_Light/infoguard_235x103_blue_light.png?width=235&height=103&name=infoguard_235x103_blue_light.png)
/Blue_Light/seehalde_235x103_blue_light.png?width=235&height=103&name=seehalde_235x103_blue_light.png)
/Blue_Light/teleinformatik_235x103_blue_light.png?width=235&height=103&name=teleinformatik_235x103_blue_light.png)
/Blue_Light/H+_235x103_blue_light.png?width=235&height=103&name=H+_235x103_blue_light.png)
/Blue_Light/DQ_235x103_blue_light.png?width=235&height=103&name=DQ_235x103_blue_light.png)
/Blue_Light/topix_235x103_blue_light.png?width=235&height=103&name=topix_235x103_blue_light.png)
/Blue_Light/head_235x103_blue_light.png?width=235&height=103&name=head_235x103_blue_light.png)
/Blue_Light/xinfra_235x103_blue_light.png?width=235&height=103&name=xinfra_235x103_blue_light.png)
/Blue_Light/pmi_235x103_blue_light.png?width=235&height=103&name=pmi_235x103_blue_light.png)
/Blue_Light/infosec_235x103_blue_light.png?width=235&height=103&name=infosec_235x103_blue_light.png)
/Blue_Light/qbits_235x103_blue_light.png?width=235&height=103&name=qbits_235x103_blue_light.png)
/Blue_Light/netaccess_235x103_blue_light.png?width=235&height=103&name=netaccess_235x103_blue_light.png)
/Blue_Light/enovate_235x103_blue_light.png?width=235&height=103&name=enovate_235x103_blue_light.png)
/Blue_Light/softec_235x103_blue_light.png?width=235&height=103&name=softec_235x103_blue_light.png)
Cloud Security Architecture: additional measures
Backups
Our operations team monitors the backup infrastructure 24/7. We understand the importance of data security, which is why we offer proactive monitoring of your backups upon request.
Web Application Firewall (WAF)
With the appropriate WAF, we can protect your cloud environments against DDoS attacks, SQL Injection, Cross-Site Scripting (XSS), or XML-based attacks like WSDL Poisoning.
Vulnerability Scanning
Our security professionals regularly assess your applications and IT infrastructures in the cloud architecture and carefully examine and evaluate any potential weaknesses or vulnerabilities.
Gateway Security
We manage and monitor your gateway protection on layer 3 and layer 4.
What our customers say

Patrick Ummel
Chief Digital Officer, Swiss Federal Audit Office
“Xelon ensures our services' secure and uninterrupted operation which is essential for us as a federal enterprise. Competent consulting, proactive support, and short response times facilitate the implementation of projects.”

Luca Franek
CEO, PMI.AG
"Besides providing all the features and functionalities relevant to us, cost transparency is what makes Xelon's platform so compelling to me. We have complete control over costs, which makes the allocation of resources and the planning of projects much easier."

Martin Scheiwiller
Owner, Tremegisto Consulting
"Setting up the client infrastructure was extremely straightforward. We were able to get the whole project up and running within three months."
Create a free account
and try Xelon HQ for yourself!
No credit card required
Cancel anytime